Last updated at Fri, 14 Mar 2025 20:05:22 GMT
Learn how external network assessment works within Vector Command, Rapid7’s continuous red team managed service.
Understanding threat exposure management
Let’s start by providing some context around where Vector Command fits into a security program and more specifically Continuous Threat Exposure Management (CTEM). Threat exposure management involves identifying, assessing, and mitigating exposures within an organization's digital environment CTEM has emerged as a dynamic program designed to address this expanding footprint and help organizations achieve a consistent and actionable security posture.
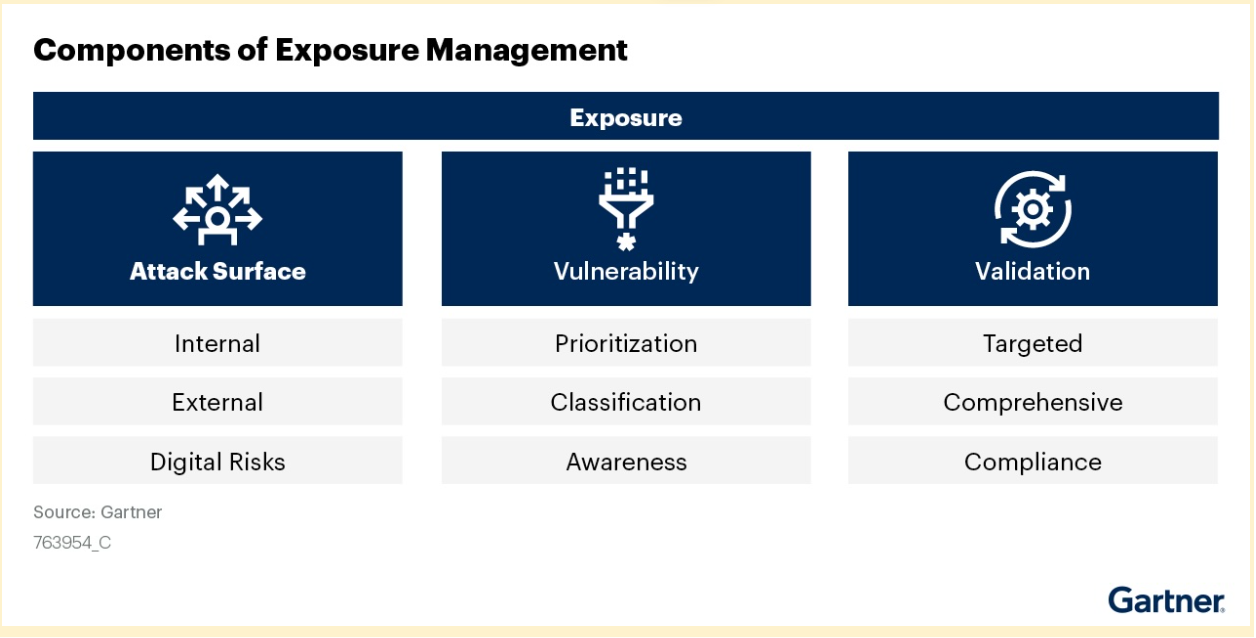
According to Gartner, some of the different technologies that can support a wider CTEM program can be organized into three distinct pillars:
“Your ‘always on’ red team”
Vector Command sits within the validation pillar, your ‘always on’ red team - validating results from technologies or services as well as validating that the controls in place are working as anticipated.
Explaining an external network assessment
An "external network assessment" refers to evaluating the security posture of an organization's publicly accessible network perimeter. This essentially simulates a hacker's perspective to identify vulnerabilities on systems and services directly reachable from the internet. This will include web servers, email servers, and exposed ports, to assess potential risks and weaknesses that could be exploited by malicious actors.
Goals of an external network assessment:
- Our red team is looking to discover potential entry points for attackers.
- Identify misconfigurations and weak security practices on exposed systems.
- Evaluate the overall security posture of the external network perimeter.
Rapid7's Vector Command red team testing approach
Our Vector Command red team experts conduct comprehensive security assessments using a multi-faceted approach:
Initial discovery and assessment
We begin by leveraging EASM-discovered assets and IVM scan results to map your approved attack surface. Our experts validate IVM findings and conduct service discovery to ensure complete coverage.
Vulnerability identification
Our team searches for common web misconfigurations through directory testing, reviews exposed administrative functions, and checks for unauthenticated access to sensitive areas. We also conduct limited, non-intrusive password testing against services like email, IAM, and VPNs using information gathered during EASM scanning.
Continuous monitoring and testing
As an always-on managed service, we:
- Perform vulnerability scans using InsightVM
- Validate potentially exploitable findings before publishing them to your portal
- Monitor Rapid7's Emergent Threat Response channels for new critical vulnerabilities
- Evaluate and test public Proof of Concept exploits when applicable
- Execute payloads to demonstrate successful breaches
- Assess credentials obtained through phishing campaigns
- Continuously retest your environment to ensure ongoing security
Throughout this process, we build comprehensive documentation of your attack landscape to inform future security assessments.
Take command of your attack surface
Rapid7 strengthens your organization's security strategy through Vector Command, delivering comprehensive CTEM alongside our other exposure management solutions.
With Vector Command, customers can now have a team of experts continuously assess their external attack surface. This includes identifying any security gaps, and receiving remediation guidance on an ongoing basis.
Our series of Vector Command blog posts will continue and next up we will cover the TTP Post-Compromise Breach Simulation.
If you would like to hear more about the world of red teaming from one of our experts behind Vector Command, Rapid7 is running a virtual session at our 2025 Take Command Summit, find out more about it here.
Learn More about Rapid7's Vector Command Service ▶︎
Validate your external attack surface exposures and test your defenses with continuous red team operations.

